“Not in my shop!”
If that’s a refrain that pops instantly to mind when you think about the possibility of monitoring your employees’ use of the internet, it may be time to rethink. Conversely, if you are a strong fan of control, you may also benefit from easing up on the reins. Somewhere between devil-may-care and iron fist is the path to enlightened management.
Regardless of the type of business you run, if there are computers on the premises and employees have regular access to them, there will be illicit uses. Even the most hard-driven office drone can manage a quick game of Solitaire, so how much more difficult it is to sneak in an hour of online shopping or a few checks on a Facebook page? Employers the world over are faced with the double query:
- What, exactly, is the danger of illicit and uncontrolled internet access in the workplace?
- Where is the fine line between monitoring and eavesdropping?

Employers should allow for individual expression or risk losing loyalty. Employees will respond better if you don’t spy on them. You need to draw the line somewhere, but where?
The answer to the first question is straightforward. If use of the internet is outside the scope required for the completion of the job at hand, that use can be considered illicit. Employers have the right to determine what employees will be permitted to do with business-owned equipment. Just as most employers would frown on an employee borrowing a copy machine for the weekend to run up a batch of holiday newsletters, the employer is paying for and owns the contract for access to the internet from computers belonging to the business. Case pretty much closed.
The several dangers of unmonitored use:
- Distraction
- Wasted time
- Waste of materials if the user is downloading and printing.
- Possible contamination of the network with downloaded viruses and other malware.
- An open door for hackers who might want to collect private information or completely shut down the network for nefarious reasons.
Here’s an example of unmonitored use gone awry:
The site was a public high school with a secure district-wide network. The employee, a classroom teacher, found her lunch period to be an excellent time for online shopping from her classroom computer. The evil-doer, later determined to be a student or group thereof, retrieved the teacher’s pass codes to both the network and her credit card using a keylogger. The personal information for every employee in the district was accessed and downloaded, and then sold. Within days, the district network of several hundred computers were at the mercy of the perpetrators who merrily hacked into the most secure corners, changing grades and creating generalized chaos. The threat of identity theft continued to hang over the employees indefinitely. The upshot of it all was that the network had to be shut down for a time, throwing record-keeping and research into chaos while the source of the problem was ferreted out by the district computer tech. Small goof; big craziness.

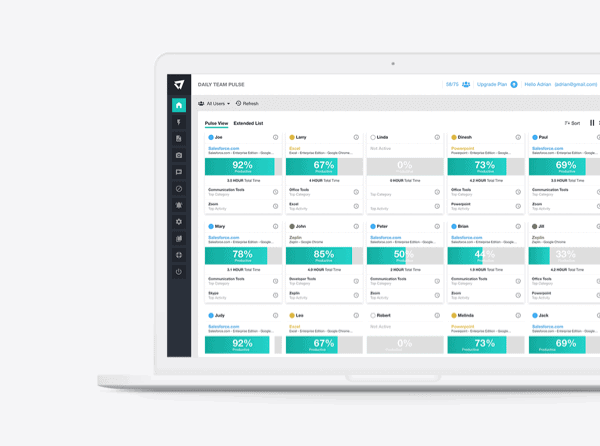
Installing an internet tracking software on your office computers will help you stop illicit uses of the internet and even possible malicious attacks.
A “keylogger” is a favored route into networks. Also called a keystroke logger or system monitor, this can be either a hardware device attached secretly to the user’s keyboard or an installed software program lurking in some or all the networked machines. The logger records every keystroke. Thus, any top-secret pass codes are rendered useless. This sort of intrusion can be prevented easily by requiring that each user change his pass code regularly on a staggered schedule, but gaining 100% compliance on a requirement of that irritation level is difficult. If internet access is monitored—including the installation by the employer of a system monitor of the same type—at very least the location of the incursion can be targeted, isolated, and disinfected more quickly.
The Problem of Wasted Time and Illicit Internet Activity
The problems of wasted time are more insidious. How many hours a day of Internet Desktop Tower Defense are you willing to support? A relaxed and focused employee is a boon, while an angry, frustrated, powerless employee is a bomb. A certain minimal investment might be worthwhile, but unregulated, the investment can go negative very quickly.
On the other hand, depending on the type of business in which your company engages, allowing employees to feed their creativity by seeking out competitors’ websites or looking up the latest patent applications while they are working on their assigned project might benefit everyone. Only someone on-site can sense the heartbeat of the organization and determine its health or relative weakness. Keeping the sense of excitement alive is one of the most valuable jobs of a manager of any type of business, no matter the number of employees.
Email and networking sites are probably the two largest draws for illegal internet use in the workplace. It is difficult, if not impossible, to completely ban the use of either. Workers have breaks in their day during which their time is their own, if only for fifteen minutes. Attempts to control the content of that time are generally doomed and may lead to revolt. The danger in permitting outside email on company computers is the risk that sensitive information may easily find its way out of the office. Networking can make strangers seem remarkably familiar, and it would be folly to assume no slips will ever sink your ship when an employee with a happy finger is instant messaging his new best buddy in Budapest.
Distraction is a huge side effect of that sort of interaction. When Mickey in Consumer Affairs is flirting online with Breezy in Accounting, what are the odds at least one order or complaint or pat on the back is going to slide by unnoticed? They’re higher than if the two of them were unable to continue their cyber affair during work hours.
Where Does Management End and Spying Begin?
The line generally becomes crystal clear when it has been crossed. If an employer makes reasonable rules, employees will respond reasonably. An employee lounge area exists in most businesses large and small. A cafeteria with a Wi-Fi connection will suffice. Allowing open access to several computers that are not networked with the workstations in the offices is an excellent, open-handed way of settling many of the problems of control. Permitting employees to use their own personal laptops, netbooks, iPhones and other smart devices is cheaper and easier all around. Once a WiFi network is in place, setting firewalls is a relatively simple and secure way of keeping the personal personal and the business stuff nice and clean. There is no such thing as “impervious,” so aim for “mostly secure,” and you will be better off than most.
Installing system monitors or keyloggers is a simple, but questionable route to take around the privacy issue. If employees are permitted access to the internet from their desks, logging their keystrokes can be an actionable invasion of privacy. After all, many of those strokes will harbor secret passwords to personal bank accounts as well as user ID’s for online gaming sites. It’s impossible to log only the keystrokes that might later be an issue.
Overall, maintaining an atmosphere of reasonable trust while allowing for safe outside use of the internet is the best of all possible solutions. As managers, employers must allow for individual expression or risk losing loyalty. As employees, workers will respond better to being made part of a team than to being spied on and smacked across the palms for infractions, real and imagined. The best arrangement will be different for each company, but there is one for every setting. Do the legwork, keep an open ear and a more open mind, and find the one that works for you.